Intel IDF 2011 Closing Keynote – Intel CTO Justin Rattner
JavaScript Physics demo
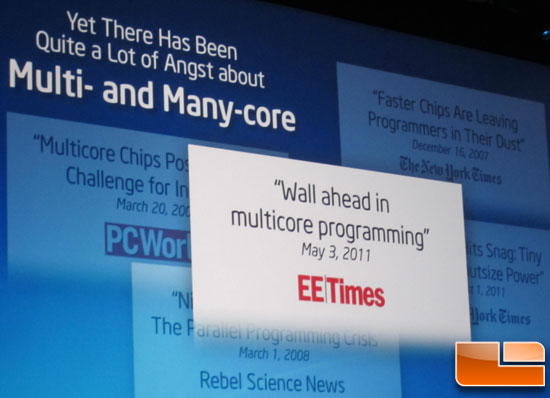
Intel says that multi- and many-core processor fears are false and
that customers are solving real problems and progress is moving forward.
Intel picked out several quotes since the Core 2 Duo processor has come
out that show negative press coverage.
You don’t have to be a ‘ninja programmer’ to actually write
applications to be able to use all the cores that are being placed on
processors.

The next guest speaker that Intel brought on stage was Brendan Eich,
who works for Mozilla, but was the creator of JavaScript. It is believed
that there will be a significant performance increase if able to
harness the power of many-core processors.

Intel showed a JavaScript Physics demo that was running 2-3 FPS and
then when using a parallel extension they showed a 15x speedup with the
demo running at roughly 45 FPS.

The demo was run on River Trail, which is open source and available on githum.com/rivertrail. This is the first public demo of parallel extension benchmark.
The third demonstration was to see if an LTE base station can be
built with a multi-core PC. Two years ago, Intel entered into a deal
with China Mobile that focused on replacing a traditional base station
hardware with 2nd generation Intel Core i7 processors and supporting
software. Intel showed off an Intel Sandy Bridge desktop system that now
serves as an LTE base station. The vector engines in the processor are
acting like Digital Signal Processors .

The next demo that they had was very cool and it dealt with facial
recognition as a biometric encryption for photos on your PC or website.
The demo was using some software called MyBookspace and the presenter
showed us how it worked with a webcam on a PC. When he was in front of
the camera it would show all the images of his friends on the social
site as the facial recognition confirmed he was the owner of the content
and the PC displayed the images.
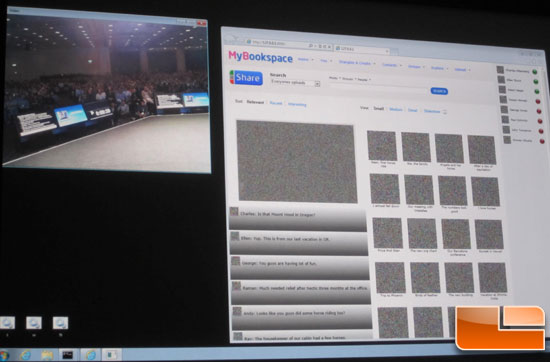
When the speaker walked away from the camera the software recognized
the fact that no one was there and removed the content so that no one
could see any of the images. The text for the images was still present,
so it doesn’t fully remove all your data.
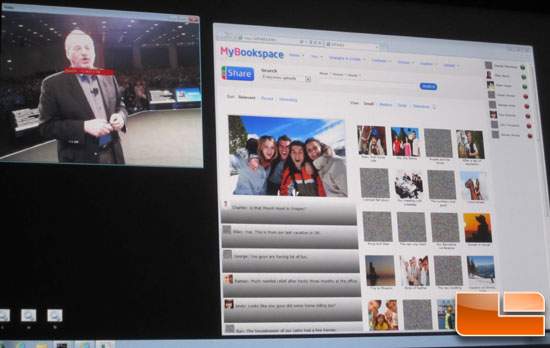
When another person walked in front of the camera the software noted
that he had access, but not to all of the images, so the system only
displayed the pictures that he was cleared to see. With people dumping
tons of images and videos onto social networking sites it will be
interesting to see how technology like this takes off. We did notice
that when two people were on the screen at once the software didn’t
really know what to do and all the images were shown. If you are at a
desk and someone walked up behind you it wouldn’t remove any content,
which appears like a weakness to us. Nonetheless, this is cool software
that has certainly has real world applications in the years to come.
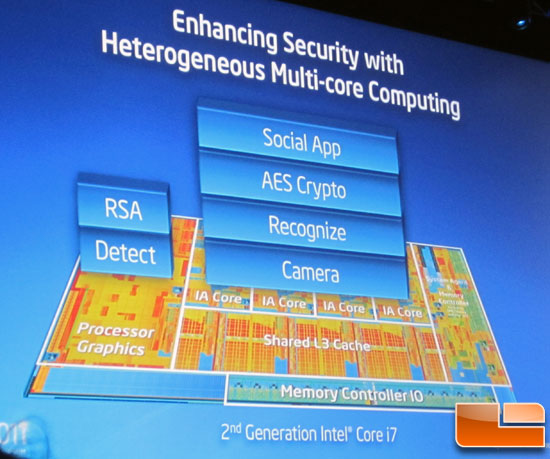
Using a processor to secure data is nothing new, but the
heterogeneous computing model where both the CPU and the GPU are being
used at the same time by a single application is still ‘new’ to many
programmers.
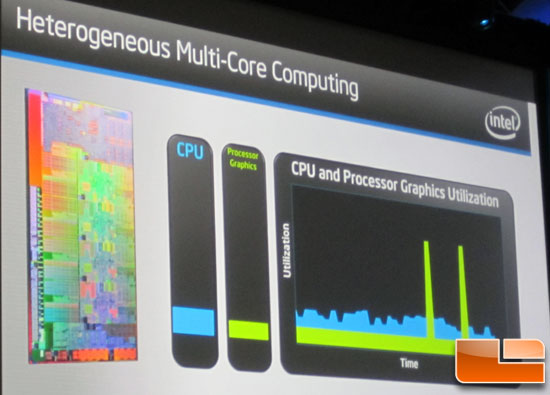
Intel also showed that their processor technology was needed to power
this software and that both the CPU and the GPU (processor graphics)
were being used. The graphics core bars spiked up real high when the
program was trying to identify a new user that came in front of the
camera and the CPU was being used to obviously deliver or blur out the
content.

Comments are closed.